System Hardening: 10 Key Steps to Secure Your Operating System
In today’s digital landscape, securing your operating system (OS) is more important than ever. As cyberattacks become more sophisticated, businesses and individuals alike must take proactive steps to protect sensitive data and system integrity. System hardening is one of the most effective strategies to reduce vulnerabilities and prevent security breaches.
System hardening, often referred to as OS hardening, involves minimizing a computer’s exposure to potential threats and implementing best practices to reduce risks. This process typically includes tightening security settings, removing unnecessary software, and applying the latest patches. With the right measures, you can strengthen your OS defenses against a wide range of cyber threats.
Here are 10 essential steps for performing system hardening, reducing the attack surface, and enhancing your OS security.

1. Clean Up Unnecessary Programs for Effective System Hardening
Every program installed on your system is a potential entry point for attackers. To reduce the risk of a security breach, remove unnecessary programs that are not vetted by your IT team. Hackers often exploit these programs to find backdoors into your system. A routine clean-up of unused software ensures that attackers have fewer ways to compromise your OS.
2. Keep Your OS Updated with Service Packs to Strengthen System Hardening
Maintaining an up-to-date OS is one of the simplest and most effective ways to secure your system. Installing the latest service packs ensures your OS benefits from the most recent security patches. Enabling automatic updates can help you stay current and avoid vulnerabilities due to outdated software.
3. Apply Critical Patches Regularly for Improved System Hardening
Patches and updates are crucial for fixing known security vulnerabilities. Many operating systems offer auto-update features, so be sure to enable them. Applying critical patches promptly can help mitigate the risks posed by newly discovered threats.
4. Implement Robust Access Control to Support System Hardening
Windows, Linux, and macOS offer powerful user account management features. By reviewing and restricting access rights, you can ensure that only authorized users have access to critical files and resources. Disable any unnecessary accounts to further reduce the potential attack surface. Restricting user permissions is a foundational aspect of system hardening.
5. Configure Your Firewall Settings
Most operating systems come with built-in firewalls. To enhance security, ensure your firewall is properly configured to block unauthorized access. If your network is connected to a corporate VPN, your IT team will likely manage a more sophisticated firewall setup, providing an additional layer of protection.
6. Disable Unused OS and Application Features
Many operating systems and applications come with features that are often unnecessary for your needs. Disabling unused functionalities helps minimize your OS’s attack surface. For example, if you don’t use Skype on your Windows machine, it’s wise to disable or uninstall it to prevent potential security holes.
7. Harden Your Network, Server, Application, and Database to Complement System Hardening
Network security is just as important as system hardening. While these tasks are generally handled by IT specialists, businesses should work with professionals to ensure that network, server, application, and database security measures are implemented. This may include encryption, firewalls, and regular security audits.
8. Use Strong Passwords and a Password Manager
A strong password is a simple but crucial defense against unauthorized access. Implementing a password manager can help you create and store complex passwords for different accounts securely. By managing passwords effectively, you reduce the risk of brute-force attacks and unauthorized logins.
9. Use Antivirus Software to Protect Your System Hardening Efforts
Ensure your system has up-to-date antivirus software that scans for and removes malicious software, including infected attachments and files. Most OS platforms come with built-in antivirus tools, but it’s important to configure them to download the latest definitions and perform regular scans.
10. Avoid Public Wi-Fi and Use VPN to Safeguard System Hardening
Public Wi-Fi networks are a common vector for cyberattacks. If you must use them, ensure you use a VPN to encrypt your traffic. For even greater security, consider using your mobile hotspot instead of connecting to a public Wi-Fi network.
Additional Best Practices for System Hardening
- Don’t leave your system unattended without locking it.
- Avoid opening suspicious email attachments or responding to unknown requests.
- Refrain from using illegal file-sharing websites, which can expose your system to malware.
- Set up a reliable data backup solution to recover your system in case of an attack.
By investing a little time in system hardening, you can significantly reduce the risk of a cyberattack. Additionally, it’s crucial to complement OS hardening with a robust data backup strategy. Should a breach occur, you’ll be able to restore your system and minimize downtime.
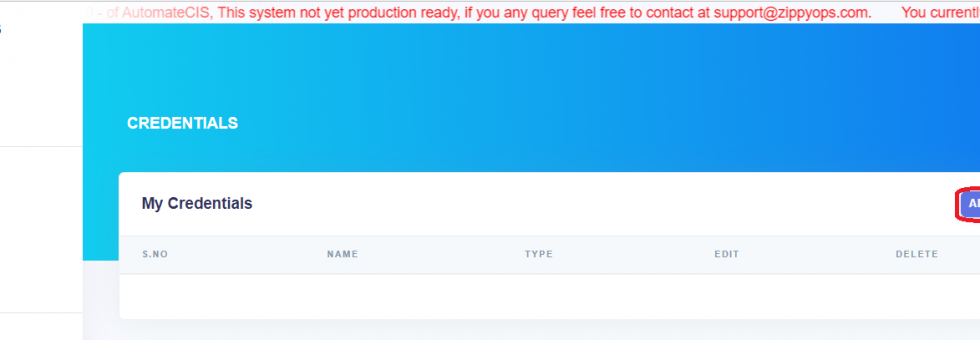
At ZippyOPS, we specialize in providing consulting, implementation, and managed services to help businesses strengthen their security infrastructure. Whether you’re looking to implement DevSecOps, AIOps, or microservices, we offer comprehensive solutions to safeguard your organization. To learn more about how we can assist with your security and operations, visit ZippyOPS Services and ZippyOPS Solutions.
For a complete overview of our offerings, check out our products page or watch informative videos on our YouTube channel.
If you’re ready to take your system security to the next level, get in touch with us at sales@zippyops.com.