Best Design Patterns for Monitoring Microservices: Ensuring Reliability & Security
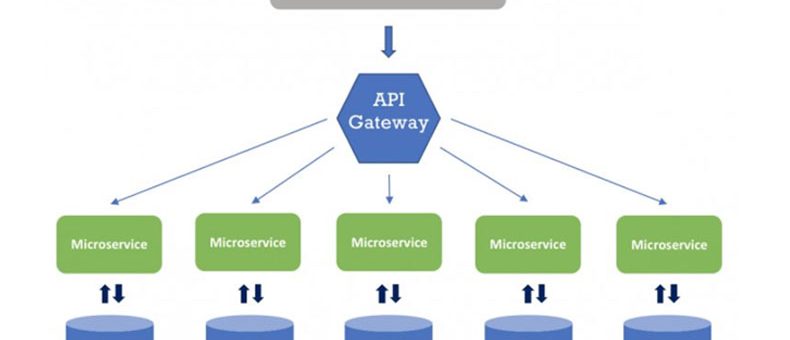
When developing microservices, it’s essential to adopt design patterns that enhance monitoring, reliability, and security. Microservices, with their distributed nature, present unique challenges compared to monolithic systems. This post explores key design patterns and tools to Monitoring Microservices and manage microservices efficiently, ensuring their stability, security, and traceability throughout their lifecycle.
The Challenges of Monitoring Microservices
In a monolithic application, monitoring is relatively straightforward. A few log statements can track the life of a request through a single service. However, in microservices architectures, where requests pass through multiple independent services, monitoring becomes much more complex. Each service may have different identifiers and logging practices, which makes tracing a request from start to finish more challenging.
To address these challenges, we need robust design patterns and tools that can handle the complexity of monitoring requests across microservices. Below, we discuss several critical areas—reliability, monitoring, and security—that need to be effectively managed to ensure smooth operations.
Ensuring Reliability in Microservices
Reliability is a cornerstone of any successful microservices architecture. Unlike traditional monolithic systems, where we could simply monitor server uptime, microservices demand more advanced techniques for fault tolerance and service availability.
1. Circuit Breakers: A Key Pattern for Reliability
Circuit breakers are essential for ensuring reliability in microservices. These patterns monitor traffic to a service and assess whether it’s responding as expected. If a service becomes unresponsive or fails to meet certain health criteria, the circuit breaker will open, preventing further traffic from reaching the failing service. This allows the system to continue operating smoothly while isolating the issue.
Kong Gateway integrates circuit breakers effectively by monitoring upstream services. Once Kong detects a failing instance, it removes it from the pool of active services until the instance becomes healthy again. This ensures high availability without overloading the network.
2. Health Checks for Continuous Monitoring
Health checks are crucial for verifying whether a service is ready to handle requests. Kong Gateway, for example, sends periodic health check requests to service instances to confirm their availability. If a service instance fails the health check, Kong will reroute traffic to healthy instances.
However, health checks introduce additional network load. If this extra burden is unacceptable, circuit breakers may be the more efficient solution.
3. Service Discovery for Seamless Operations
Service discovery is another vital aspect of ensuring reliability in a microservices architecture. Using a service mesh, such as Kuma, allows services to automatically discover and communicate with each other, regardless of their network location or health status. Kuma handles dynamic changes like service scaling and instance failures without requiring manual intervention. This makes the network more resilient and transparent to users.
Monitoring Microservices for Optimal Performance
Once reliability is established, it’s time to focus on monitoring. In the world of microservices, traditional monitoring strategies don’t suffice. A more advanced approach, like distributed tracing, is necessary to track a request’s journey across multiple services.
4. Distributed Tracing: A Window into Service Performance
Distributed tracing allows you to track requests as they flow through different microservices. Tools like Kong Gateway support Zipkin, a distributed tracing system that assigns unique trace IDs to requests and sub-requests. These IDs allow you to trace a request from its entry point to its final destination, even if it interacts with multiple services along the way.
Kuma also supports tracing through Zipkin and Datadog, providing detailed insights into each service call. By integrating tracing into your microservices architecture, you can quickly pinpoint performance bottlenecks or identify slowdowns in the system.
5. Centralized Logging for Simplified Debugging
In microservices, logs are often scattered across various services, making it difficult to piece together a request’s full journey. Centralized logging allows you to aggregate logs from multiple sources into a single dashboard for easy analysis.
By using tools like Grafana Loki alongside Kong Gateway and Kuma, you can view all logs related to a single request in one place. This visibility simplifies troubleshooting, ensuring that you can identify and resolve issues quickly.
Security Considerations in Monitoring Microservices
Security in microservices requires attention both at the network level and within the services themselves. Here are two critical security patterns to consider:
6. HTTPS/TLS for Secure External Communication
Secure communication between services is a fundamental aspect of a microservices architecture. Kong Gateway facilitates the use of TLS (Transport Layer Security) for encrypting external traffic. By using the ACME plugin, Kong can automatically manage and renew TLS certificates, ensuring that your external communication remains secure.
7. Micro-Segmentation for Internal Security
Micro-segmentation involves dividing microservices into different security zones, restricting which services can communicate with each other. Using Kuma, you can define traffic permissions between services, ensuring that only authorized services can interact with sensitive components, like payment processing systems.
In addition, Kuma supports mTLS (mutual TLS), which verifies the identity of both the client and the server before establishing an encrypted connection. This enhances security by ensuring that only trusted services can communicate with each other, further protecting sensitive data.
Conclusion: Achieving Reliable, Secure, and Traceable Microservices
To build a reliable, secure, and traceable microservices architecture, it’s essential to adopt the right design patterns and tools. By utilizing Kong Gateway and Kuma, you can enhance service reliability with circuit breakers, health checks, and service discovery. For monitoring, distributed tracing and centralized logging allow you to track requests across services, while security measures like TLS, micro-segmentation, and mTLS ensure robust protection for your system.
As the complexity of microservices grows, consider leveraging expert consulting and managed services from ZippyOPS. ZippyOPS provides comprehensive solutions in DevOps, DataOps, Cloud, and MLOps to help organizations implement best practices for microservices architecture, ensuring high availability, security, and seamless monitoring. Learn more about our services here and explore our solutions tailored for your needs.
For expert guidance and implementation, reach out to us at sales@zippyops.com.



