IT and OT Security: Why Both Are Crucial for Your Organization
In today’s interconnected world, the importance of IT and OT security cannot be overstated. While information technology (IT) typically focuses on protecting an organization’s digital infrastructure, operational technology (OT) safeguards the physical devices used in industries like manufacturing. A robust cybersecurity strategy should protect both IT and OT to ensure an organization’s resilience against growing cyber threats.
As cyberattacks become more sophisticated, organizations must address both IT and OT vulnerabilities. Below, we explore why a balanced approach to IT and OT security is essential and how businesses can navigate the growing challenges of securing these two critical areas.
The Rise of Industrial Connectivity and Cybersecurity Risks
The rapid growth of the Industrial Internet of Things (IIoT) presents both opportunities and challenges. According to a recent report, the global IIoT market, valued at $263 billion in 2020, is projected to exceed $1 trillion by 2028. Many businesses are turning to IIoT devices to increase productivity, reduce costs, and minimize errors.
However, this expansion comes with a significant increase in cyberattack risks. A 2021 study revealed that 44% of organizations had experienced a cyberattack involving an IoT or OT device, with nearly half reporting a surge in such incidents over the past 12-24 months. Cybercriminals often target vulnerable devices, using them as entry points for broader attacks. This makes it essential to integrate both IT and OT security into a comprehensive strategy.
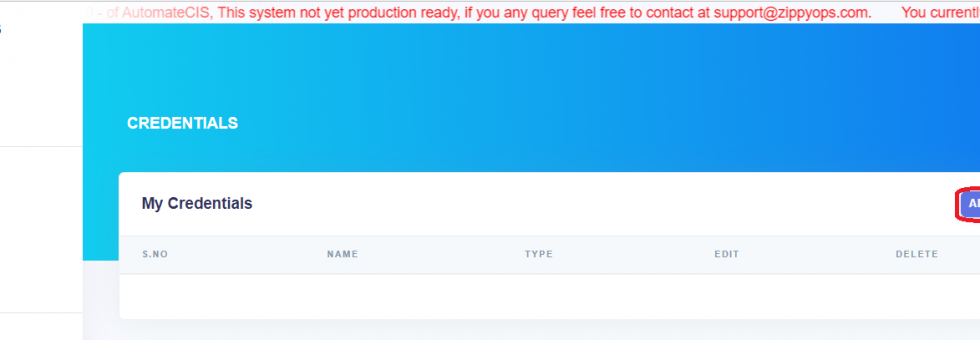
At the same time, ZippyOPS offers a range of services to help organizations strengthen their IT and OT security frameworks. Whether through consulting, implementation, or managed services, ZippyOPS is well-equipped to support your security needs. Explore more about how ZippyOPS can assist with DevSecOps, DataOps, Cloud security, and AIOps for a seamless IT-OT cybersecurity approach: ZippyOPS Services.
Why Segmentation Alone Isn’t Enough
Historically, IT and OT departments have operated in silos, each focused on their own distinct responsibilities. However, this separation can create security vulnerabilities. Cybersecurity expert Rick Driggers emphasizes that IT teams must understand the OT environment to safeguard the entire organization. This includes knowing what OT assets exist, ensuring they are correctly configured, and maintaining consistent security policies.
Collaboration between IT and OT teams is vital to mitigating risks. However, it’s not always easy. Both teams may have different priorities and ways of thinking, making collaboration a challenge. Therefore, companies must focus on fostering a shared understanding between teams. One effective approach is to hold regular meetings where both groups can align their goals and address common security concerns.
ZippyOPS can help organizations bridge the gap between IT and OT by offering tailored solutions. With expertise in cloud infrastructure, microservices, and security protocols, ZippyOPS ensures your teams work together to enhance overall resilience. Learn more about our solutions: ZippyOPS Solutions.
IT and OT Security’s Impact on Reputation
In today’s digital age, a company’s reputation is invaluable. A cyberattack that impacts both IT and OT systems can severely damage an organization’s image. For instance, an attack on the email and order management system might disrupt communication with customers, leading them to perceive the company as unreliable. Similarly, a breach in OT systems could jeopardize production quality, potentially causing defects and even safety hazards.
As cyberattacks become more frequent, protecting both IT and OT systems is not just a technical necessity but a business imperative. Organizations with strong security measures in place can avoid such repercussions, thereby preserving their reputation and ensuring customer trust.
Ransomware: A Growing Threat to IT and OT Security
Ransomware attacks continue to rise, making IT and OT security even more critical. These attacks can cause substantial data loss and disrupt operations for days or weeks. According to a 2020 study, 56% of organizations affected by ransomware paid the ransom, but only 29% managed to fully restore their data. This highlights the importance of a proactive cybersecurity strategy that addresses both IT and OT vulnerabilities.
Even when companies have implemented proactive measures, ransomware can still slip through. This underscores the need for integrated security across IT and OT environments. ZippyOPS can help businesses implement comprehensive vulnerability management strategies that include MLOps, DevOps, and Automated Ops to detect and mitigate threats before they escalate. Discover more about our products here: ZippyOPS Products.
IT and OT Security: A Unified Approach is Essential
In conclusion, the security of both IT and OT systems is critical for safeguarding an organization’s operations, reputation, and bottom line. The convergence of IT and OT security helps businesses identify vulnerabilities, respond quickly to threats, and ensure long-term resilience. With the increasing threat landscape, investing in both areas is no longer optional but a necessity for modern organizations.
ZippyOPS offers tailored consulting and implementation services to help your business create a unified security strategy. By focusing on DevSecOps, DataOps, and AIOps, we help organizations protect their IT and OT environments effectively. Reach out to ZippyOPS for more information: sales@zippyops.com.