Cybersecurity Challenges App Developers Must Address Today
Cybersecurity challenges are growing faster than most development teams can react. As applications become more connected, attackers gain more opportunities. Because of this shift, app developers now play a direct role in protecting users, data, and infrastructure.
Modern security is no longer an afterthought. Instead, it must be designed, tested, and automated throughout the development lifecycle. When security is ignored early, fixing issues later becomes costly and risky.

Why Cybersecurity Challenges Are Increasing for App Developers
Cyber threats evolve alongside technology. At the same time, businesses deploy new tools, cloud platforms, and integrations at record speed. As a result, attackers constantly look for gaps before teams can close them.
According to the Verizon Data Breach Investigations Report, human error, misconfigurations, and credential abuse remain leading causes of breaches. This reality shows why secure development practices matter more than ever.
Cybersecurity Challenges in Remote and Hybrid Work Environments
Expanded Attack Surface Across Devices and Cloud
Remote work has permanently changed how systems operate. Employees now access applications from personal devices, home networks, and cloud platforms. Consequently, the attack surface has grown far beyond the traditional office network.
Multi-cloud environments also increase complexity. Every new service, API, or integration introduces potential weaknesses. Because of this, app developers must design applications with secure access, identity controls, and visibility in mind.
ZippyOPS helps organizations manage these environments through secure cloud architecture, infrastructure automation, and DevSecOps practices. Their consulting and managed services ensure security remains consistent across hybrid and multi-cloud setups. Learn more at https://zippyops.com/services/.
Social Engineering as a Persistent Cybersecurity Challenge
Why People Remain the Primary Target
“Professionals hack people, not systems.” This statement still holds true today. Social engineering attacks succeed because they exploit trust, not technology.
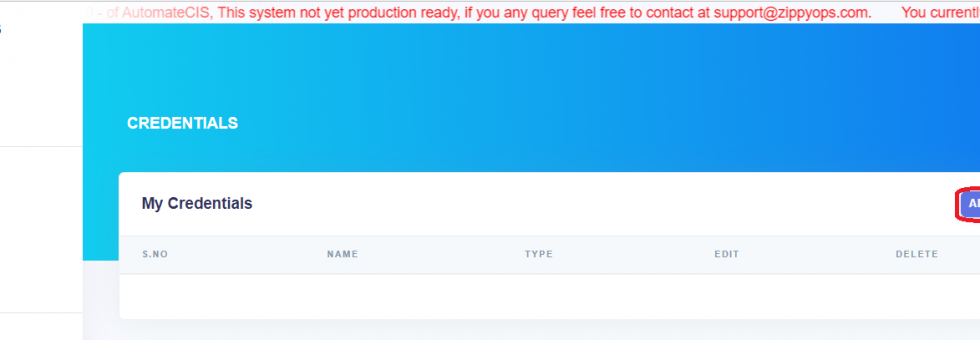
Phishing emails, fake login pages, and impersonation attacks often bypass advanced security tools. Therefore, developers must assume that credentials can be compromised and design systems that limit damage.
For example, strong authentication, least-privilege access, and behavioral monitoring can reduce risk. At the same time, secure application workflows help prevent lateral movement after an initial breach.
Understaffed Security Teams and Developer Responsibility
Security Gaps Caused by Talent Shortages
Many organizations struggle to hire and retain cybersecurity professionals. As a result, development teams often absorb additional security responsibilities without enough support.
Long hours and constant incident response also lead to burnout. Consequently, automation becomes essential. Secure CI/CD pipelines, automated testing, and policy-as-code help reduce manual effort while improving consistency.
ZippyOPS supports teams by implementing automated operations, AIOps, and MLOps solutions that reduce operational load. Their solutions help teams detect issues early and respond faster. Explore these capabilities at https://zippyops.com/solutions/.
Cybersecurity Challenges in Data Management and Compliance
Protecting Data Across Regions and Regulations
Data protection has become more complex due to global privacy laws. Businesses must understand where sensitive data lives and how it moves through systems. Without visibility, breaches become harder to contain.
Ransomware remains a major threat because it disrupts access to critical data. Therefore, secure backups, encryption, and recovery plans are no longer optional.
Effective DataOps practices improve governance and resilience. With proper automation, teams can track data flows, enforce policies, and recover quickly after incidents.
ZippyOPS products support secure data pipelines, infrastructure visibility, and automated recovery. You can explore available tools at https://zippyops.com/products/.
Why Cybersecurity Challenges Will Continue to Evolve
Threats do not stand still. Misconfigurations, poor security hygiene, and outdated practices still cause many breaches. Meanwhile, attackers refine techniques that rely on speed and deception.
Artificial intelligence and automation will shape the future of security. However, tools alone are not enough. Secure design, continuous monitoring, and integrated DevSecOps practices will define successful teams.
ZippyOPS combines consulting, implementation, and managed services across DevOps, DevSecOps, Cloud, Automated Ops, Microservices, Infrastructure, and Security. Their practical approach helps teams build secure systems without slowing innovation. For real-world demos and insights, visit their YouTube channel at https://www.youtube.com/@zippyops8329.
In Summary: Turning Cybersecurity Challenges into Strengths
Cybersecurity challenges affect every stage of application development. However, with the right mindset and tools, developers can reduce risk while delivering value faster.
Security must be continuous, automated, and shared across teams. When done right, it becomes a competitive advantage instead of a bottleneck.
If you want expert guidance on building secure, scalable systems, contact ZippyOPS at sales@zippyops.com to start the conversation.