15 API Security Best Practices Every Developer Should Follow
APIs (Application Programming Interfaces) are essential tools that connect software applications, allowing them to share data and functionality. However, improper security measures can expose sensitive information and create vulnerabilities. In this guide, we explore API security best practices that developers can implement to safeguard their applications and maintain user trust.

Why API security best practices Should Be a Top Priority
Protect Sensitive Data
APIs frequently handle sensitive information, including personal details, payment information, and health records. A security breach can lead to data theft, identity fraud, or other costly consequences. Therefore, safeguarding API endpoints is critical for both developers and users.
Ensure Compliance and Regulatory Standards
Industries like finance, healthcare, and government must meet strict regulations such as GDPR, HIPAA, or PCI-DSS. By following security guidelines, developers can avoid legal penalties while maintaining customer confidence.
Preserve Brand Reputation
Security incidents can harm a company’s reputation and erode customer trust. Consumers expect their data to be secure when interacting with applications. Consequently, developers must implement strong API security measures to protect brand integrity.
Prevent Financial Losses
Cyberattacks can result in direct financial losses, legal fees, and costs for incident response. Implementing API security best practices reduces the risk of costly breaches.
Stay Ahead of Evolving Cyber Threats
Cyber threats are increasingly sophisticated. Therefore, continuous monitoring and adopting proactive security practices are essential to defend applications from attacks.
15 API Security Best Practices
1. API security best practices of Strong Authentication and Authorization
- Use multi-factor authentication and strong passwords.
- Apply role-based access control (RBAC) to manage user permissions.
- Leverage OAuth2 or OpenID Connect for secure authorization.
2. API security best practices of Enforce HTTPS and Certificate Pinning
Ensure all API traffic uses HTTPS to prevent eavesdropping. Certificate pinning can further protect against spoofing attacks.
3. Input Validation and Sanitization
Validate all input data and sanitize entries to prevent injection attacks. Parameterized queries can help avoid SQL injection.
4. API Keys and Token Management
Limit access to resources with API keys and revoke them when necessary. Use short-lived access tokens to reduce risks if compromised.
5. Encryption and Secure Storage
Encrypt data both in transit (TLS) and at rest. Hash sensitive information such as passwords for added security.
6. Logging and Monitoring
Track API usage with logs and employ Security Information and Event Management (SIEM) tools to detect anomalies.
7. Secure Coding Practices
Follow secure development principles including input validation, output encoding, error handling, and defense-in-depth strategies.
8. Integrate Security into SDLC
Incorporate security early in the development lifecycle. This proactive approach reduces vulnerabilities and streamlines compliance.
9. Regular Updates and Patching
Keep APIs and dependencies up to date. Use automated tools to detect vulnerabilities and apply patches promptly.
10. Vet Third-Party Libraries
Ensure external libraries are secure and updated regularly. Avoid using outdated packages that could introduce risks.
11. Design APIs with Security in Mind
Apply security principles from the design phase. Industry standards like OAuth2 and OpenID Connect should guide authentication and authorization.
12. API Gateway Implementation
Use an API gateway to manage traffic, enforce rate limits, and implement security controls consistently.
13. Short-Lived Access Tokens
Minimize the impact of compromised tokens by issuing tokens with limited lifespans.
14. Clear Documentation for Secure Use
Provide documentation outlining authentication methods, rate limits, and response codes. This guidance helps developers maintain secure API integration.
15. API security in Regular Security Testing
Conduct penetration testing, vulnerability scanning, and code audits to detect and address potential threats proactively.
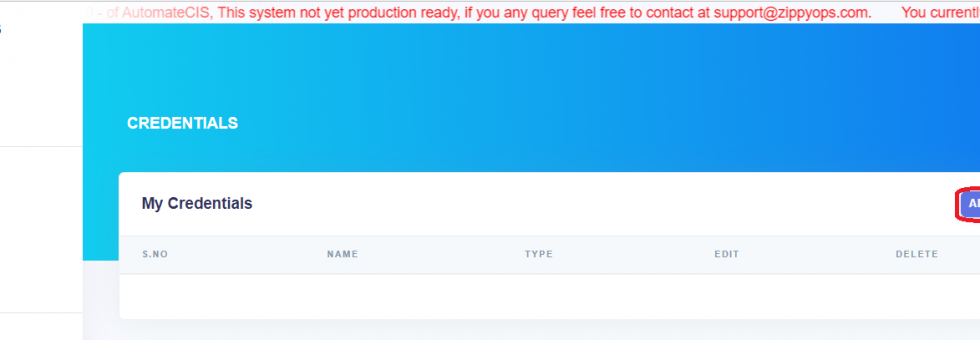
How ZippyOPS Supports API security best practices
At ZippyOPS, we help organizations implement DevOps, DevSecOps, Cloud, Automated Ops, AIOps, MLOps, Microservices, Infrastructure, and Security solutions. Our services include consulting, implementation, and managed operations that strengthen API security across all development stages. Developers can explore our offerings here: ZippyOPS Services, Solutions, and Products.
For additional guidance, ZippyOPS also provides educational content through our YouTube channel, showcasing practical demos and security insights.
Conclusion for API security best practices
API security is not optional—it is essential for protecting sensitive data, ensuring compliance, and maintaining user trust. By applying these 15 API security best practices, developers can significantly reduce vulnerabilities, prevent breaches, and deliver reliable applications.
For expert guidance on implementing secure and scalable APIs, contact ZippyOPS at sales@zippyops.com for a consultation.