Browser-in-the-Browser Attack: How to Detect and Prevent It
Phishing has evolved. While classic scams are easy to spot, hackers now use sophisticated tricks like the browser-in-the-browser attack. This method involves a fake single sign-on (SSO) login window, which can fool even experienced users. However, understanding how it works and using proper safeguards can keep your accounts secure.

What Is a Browser-in-the-Browser Attack?
A browser-in-the-browser attack occurs when a simulated SSO window appears while logging in or creating an account. Users might see familiar login options, such as Google, Facebook, or Apple. Yet, this window is entirely fake — created with HTML, CSS, and JavaScript to mimic the real interface.
Unlike traditional phishing, the BitB popup doesn’t alter the URL bar. Because of this, even vigilant users might enter their credentials, unknowingly giving hackers access. Once stolen, these login details can compromise multiple accounts, exposing sensitive information like payment details. According to Verizon’s Data Breach Investigations Report, over 90% of breaches start with phishing.
How a Browser-in-the-Browser Attack Works
Attackers first design a legitimate-looking website, often a job portal or media service. When users attempt to sign up, a fake SSO popup appears.
To make these popups convincing, hackers use templates resembling real login windows from Google, Apple, or Facebook. With JavaScript and jQuery, the fake window overlays the page, tricking users into entering credentials. In essence, the BitB attack is a digital sleight of hand.
Detecting a Browser-in-the-Browser Scam
You don’t need to fall victim. Follow these strategies to spot BitB attacks:
1. Use a Password Manager
Password managers only fill credentials in legitimate SSO windows. If the login box stays empty, it’s a clear warning.
2. Drag the Login Window
A genuine SSO window can move freely over the browser interface. If the popup is stuck behind the address bar, it’s likely a BitB attack.
3. Minimize the Main Browser Window
If the login popup disappears when you minimize the main browser, it’s not real. Legitimate SSO windows remain separate.
4. Install NoScript
NoScript blocks JavaScript and other executable content. This can prevent BitB popups while also enhancing overall web security.
Protecting Yourself Against BitB Attacks
Besides spotting fake windows, enabling two-factor authentication (2FA) on all accounts adds another layer of protection. Even if credentials are stolen, hackers cannot log in without the second factor.
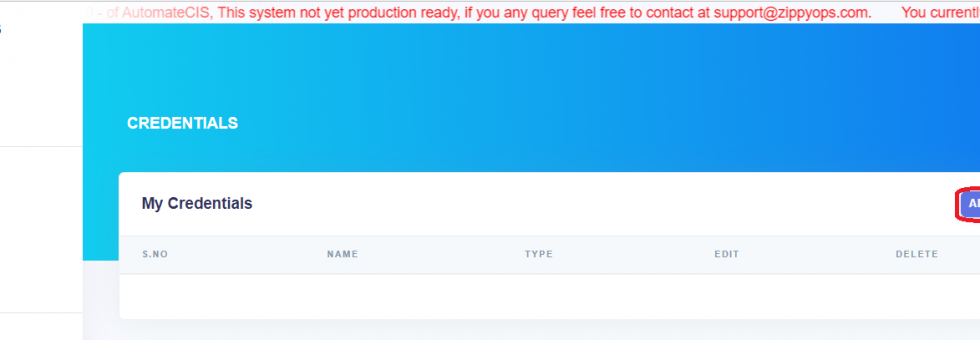
Moreover, organizations can adopt automated operations, cloud solutions, and secure microservices to minimize phishing risks. ZippyOPS offers consulting, implementation, and managed services in areas such as DevOps, DevSecOps, DataOps, Cloud, Automated Ops, AIOps, MLOps, Microservices, Infrastructure, and Security. These solutions help companies build resilient, secure environments that reduce the risk of attacks like BitB. Learn more about our services, solutions, and products. For video demos, check our YouTube channel.
Conclusion
Browser-in-the-browser attacks are subtle but preventable. Always check popups, use password managers, enable 2FA, and employ browser security tools. For businesses, integrating DevOps, secure microservices, and automated monitoring with ZippyOPS can protect both users and infrastructure from phishing threats.
For more information or to schedule a consultation, reach out to sales@zippyops.com.