Containerization Journey: Transform Monoliths to Microservices
Modern software delivery demands agility, scalability, and resilience. The containerization journey offers a proven path to transform monolithic applications into modular, independently deployable microservices. This process enhances deployment speed, fault tolerance, and operational efficiency.
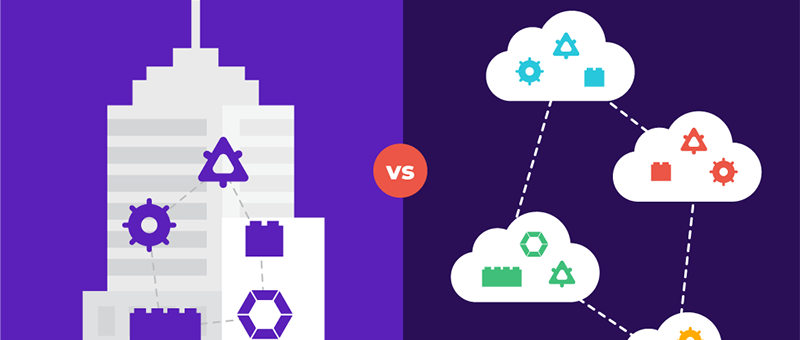
Traditionally, applications were built using monolithic architecture, where all components were tightly integrated and deployed as a single unit. While this approach worked initially, its limitations became apparent as applications grew in complexity and organizations increasingly relied on distributed systems.
Containerization emerged to address these challenges, enabling applications to be broken down into loosely coupled microservices. This approach allows developers to deploy changes quickly, scale specific services independently, and improve fault isolation.
In this article, we explore the limitations of monolithic architecture, the benefits of containerization, and the practical steps organizations can take to embrace this transformation.
Breaking a Monolith Into Microservices
A microservices architecture divides applications into small, modular services that communicate through APIs. Unlike monoliths, microservices offer fault tolerance since the failure of one service does not impact the entire system. They also enable polyglot persistence, allowing each service to select its optimal storage solution.
Before starting the migration, it is essential to understand the differences between monolithic and microservices architectures to determine the best transformation strategy.
| Aspect | Monolithic Architecture | Microservices Architecture |
|---|---|---|
| Structure | Single, large application | Multiple, small services |
| Deployment | Deploy entire application at once | Deploy services independently |
| Scalability | Scale entire application | Scale specific services as needed |
| Development | Changes require full coordination | Changes can be made independently |
| Technology stack | Single, unified stack | Each service can use different stacks |
| Fault tolerance | Failure affects entire app | Failure has limited impact |
Understanding these differences helps organizations select a migration approach that aligns with their goals and resources.
containerization journey in Strategies for Migrating to Containers
Migration strategies vary based on organizational goals. Each approach provides a roadmap to shift from monoliths to containerized microservices while balancing risk, resources, and business priorities.
Phased Approach
The phased approach incrementally breaks monoliths into microservices, starting with components likely to yield the greatest benefits. Teams gain experience while minimizing disruption.
When to use: Best for organizations with limited resources or complex applications that require gradual transformation.
Hybrid Architecture
Hybrid architecture keeps some components in the monolith while migrating others to microservices. This balances stability with flexibility and allows organizations to adopt microservices progressively.
When to use: Ideal for businesses that want partial migration without fully dismantling their monolith.
Big Bang Approach
The big bang strategy redesigns the entire application using microservices from scratch. It demands resources and carries risk but unlocks full microservices and container benefits.
When to use: Suitable for applications needing complete overhaul or organizations with the capacity to manage a full-scale transition.
Re-Platforming
Re-platforming moves a monolith to a container environment without immediate decomposition into microservices. It provides some benefits of containerization with lower complexity.
When to use: Recommended for organizations new to containers or those seeking incremental gains before full migration.
Practical Steps to Embracing a Containerization Journey
A successful containerization journey requires a structured approach to transform monoliths into scalable microservices. The following steps outline a practical roadmap.
1. Identify Application Components
Analyze your application architecture to identify components like databases, web servers, and background workers. Understanding dependencies ensures efficient resource allocation and modular deployment.
Purpose:
- Clarify architecture and dependencies
- Enable component isolation
- Streamline communication between containers
2. Containerize Application Components
Use Docker or other container technologies to package each component into isolated environments. Follow best practices such as multi-stage builds, non-root users, and optimized image sizes. Store images in registries like Docker Hub or RedHat Quay.
Purpose:
- Facilitate portability and deployment
- Enable version control
- Maintain isolated, reproducible environments
3. Container Orchestration
Leverage Kubernetes, Docker Swarm, or other orchestration platforms to manage deployment, scaling, and health monitoring. Define resource limits, implement self-healing mechanisms, and enable rolling updates.
Purpose:
- Optimize resources
- Ensure high availability
- Simplify updates and rollbacks
4. Container Management and Security
Integrate monitoring tools such as Prometheus and Grafana, implement CI/CD pipelines, and enforce container security best practices like vulnerability scanning, network segmentation, and least privilege.
Purpose:
- Monitor performance and resource usage
- Maintain security standards
- Implement proactive logging and alerting
For organizations seeking expert guidance in DevOps, DevSecOps, DataOps, Cloud, Automated Ops, MLOps, Microservices, Infrastructure, and Security, ZippyOPS provides consulting, implementation, and managed services. Explore their solutions and products to accelerate containerization adoption. For demonstrations and tutorials, check ZippyOPS YouTube.
Real-World Use Cases of Containerization Journey
Several companies have leveraged containerization and microservices for operational efficiency and scalability:
- Netflix: Transformed its monolithic streaming platform into modular services to manage peak traffic and improve deployment agility.
- Spotify: Improved developer productivity by breaking up a monolith into containerized services, enabling independent, iterative work.
- Uber: Adopted Domain-Oriented Microservice Architecture (DOMA) with containers, achieving scalable deployments and fault isolation during traffic spikes.
For reference, CNCF’s containerization guide provides industry insights into container adoption and orchestration practices.
Conclusion of Containerization Journey
The containerization journey empowers organizations to convert monolithic applications into agile, scalable, and resilient microservices. While challenges such as distributed system complexity may arise, the benefits of modularity, faster deployments, and improved fault tolerance are substantial.
Key considerations for your transformation include:
- Identifying components that benefit most from containerization
- Selecting the appropriate migration strategy: phased, hybrid, big bang, or re-platforming
- Ensuring robust container orchestration and security practices
With the roadmap in place, the next step is implementation, monitoring, and iterative refinement. For guidance, consulting, and managed services across DevOps, Cloud, Microservices, and Security, contact ZippyOPS at sales@zippyops.com.



