Breach and Attack Simulation: Building Resilient Cyber Defense
As the cybersecurity landscape grows more complex, organizations face constant pressure to prove that their security investments actually work. Breach and Attack Simulation helps security teams validate defenses, expose gaps, and strengthen resilience before real attackers strike.
Today’s enterprises operate across hybrid and multi-cloud environments. At the same time, they rely on distributed networks, SaaS platforms, remote users, and IoT devices. Because of this complexity, even a small misconfiguration can open the door to a serious breach. As a result, traditional security testing alone is no longer enough.
Why Breach and Attack Simulation Matters Today
Cyber threats are no longer simple or predictable. Attackers test environments continuously, adapting their methods to bypass controls. However, many organizations still rely on point-in-time assessments that quickly become outdated.
Breach and Attack Simulation solves this problem by continuously testing real-world attack paths. Instead of guessing where weaknesses exist, security teams gain clear evidence of what works and what fails. Consequently, leaders can make informed decisions about risk and spending.
According to Gartner, BAS tools allow enterprises to simulate the full attack lifecycle, including lateral movement and data exfiltration, in a safe and controlled way. This approach improves visibility and accountability across security programs.
External reference: https://www.gartner.com/en/information-technology/glossary/breach-and-attack-simulation-bas
Limitations of Traditional Security Testing
Many organizations still depend on established testing methods. While these remain valuable, they also come with clear limitations.
Penetration Testing
Penetration testing uncovers vulnerabilities using skilled testers and real attack techniques. However, it is expensive and usually limited in scope. Moreover, it provides only a snapshot in time.
Red, Blue, and Purple Teaming
Red teams simulate attackers, while blue teams defend systems. Purple teams align both efforts. Although effective, these exercises require significant coordination and skilled resources. Therefore, they are difficult to run frequently.
The Core Challenge
All traditional approaches are largely manual. Because environments change daily, their findings lose relevance quickly. As a result, security teams struggle to maintain continuous assurance.
What Is Breach and Attack Simulation?
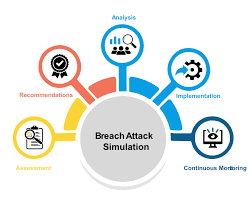
Breach and Attack Simulation is a security validation approach that continuously tests defenses by safely simulating real attack techniques. These simulations mirror how modern attackers operate, without disrupting production systems.
BAS platforms automate attack execution, validate security controls, and highlight gaps across networks, endpoints, cloud, and applications. At the same time, they complement penetration testing rather than replacing it.
Core Functions of Breach and Attack Simulation
BAS platforms focus on four essential capabilities:
- Attack: Safely simulate real-world threats
- Visualize: Show exposed paths and weak points
- Prioritize: Rank risks based on business impact
- Remediate: Guide teams toward effective fixes
Because BAS uses closed-loop automation, security teams can test continuously instead of reacting after incidents occur.
Types of Breach and Attack Simulation Technologies
Agent-Based Simulation
Lightweight agents run on endpoints to assess vulnerabilities from inside the network. This approach reveals realistic attack paths that external scans often miss.
Malicious Traffic Simulation
These tools generate simulated attack traffic between virtual machines. As a result, teams can validate detection and prevention controls without real malware.
Multi-Vector Attack Simulation
This advanced approach combines internal and external techniques. It closely mirrors real attacker behavior across cloud, endpoint, and network layers.
Critical Capabilities to Look for in Breach and Attack Simulation Platforms
An effective Breach and Attack Simulation solution should deliver:
- Continuous and automated simulations
- Coverage across the cyber kill chain
- Risk-based scoring and prioritization
- Clear dashboards and visual reports
- Safe execution in production environments
- Support for hybrid, multi-cloud, and on-prem setups
In addition, strong alignment with frameworks such as MITRE ATT&CK helps teams communicate findings clearly.
Real-World Use Cases for Breach and Attack Simulation
Security Posture Assessment
BAS provides ongoing visibility into how defenses perform against current threats. Therefore, teams can validate readiness across cloud, containers, endpoints, and email systems.
Control Validation
By simulating attacks, organizations confirm whether tools are properly configured. Consequently, configuration drift is detected early.
Mergers and Acquisitions
BAS helps assess the security posture of acquisition targets. This insight reduces post-merger risk and speeds up integration.
Third-Party Risk Assessment
Because BAS does not expose sensitive data, it enables safer validation of partner security controls.
Risk-Based Vulnerability Management
BAS identifies which vulnerabilities are most likely to be exploited. As a result, remediation efforts focus on what truly matters.
Red and Purple Team Enablement
Automation allows teams to scale testing, improve realism, and track progress over time.
SOC Performance Measurement
Metrics such as MTTD and MTTR become measurable. Therefore, leaders can prove operational improvements with data.
Actionable Threat Intelligence
Threat intelligence becomes practical when validated through simulation. This transforms insights into action.
Breach and Attack Simulation in Modern Cloud and DevSecOps
As organizations adopt DevOps and DevSecOps, security must shift left and run continuously. Breach and Attack Simulation aligns naturally with CI/CD pipelines, cloud-native platforms, and microservices.
ZippyOPS supports this transformation by delivering consulting, implementation, and managed services across DevOps, DevSecOps, Cloud, Automated Ops, AIOps, MLOps, DataOps, Infrastructure, and Security. By integrating BAS into these workflows, organizations gain continuous security validation without slowing innovation.
Learn more about ZippyOPS capabilities:
- Services: https://zippyops.com/services/
- Solutions: https://zippyops.com/solutions/
- Products: https://zippyops.com/products/
- Videos: https://www.youtube.com/@zippyops8329
Future Outlook for Breach and Attack Simulation
The BAS market continues to grow as security leaders demand measurable outcomes. Future advancements will focus on cloud-native environments, Zero Trust alignment, SOAR integration, and AI-driven simulations.
As attack surfaces expand, Breach and Attack Simulation will remain a cornerstone of proactive cyber defense.
Conclusion: Turning Security Insight into Action
Breach and Attack Simulation helps organizations move from reactive defense to continuous validation. By safely simulating real attacks, teams gain clarity, reduce risk, and improve confidence in their security posture.
When combined with strong DevSecOps practices and expert guidance, BAS becomes a force multiplier. ZippyOPS helps organizations adopt and operationalize these capabilities across cloud, infrastructure, and security ecosystems.
To explore how Breach and Attack Simulation can strengthen your cyber defense, contact sales@zippyops.com.


