State-Sponsored Cyberattacks: From Ransomware to Ransom Nations
State-sponsored cyberattacks are no longer isolated incidents—they have become a major global security concern. From ransomware targeting individuals to nation-level operations, understanding these threats is crucial for businesses, governments, and cybersecurity teams.
What Are State-Sponsored Cyberattacks?
State-sponsored cyberattacks are digital operations orchestrated or supported by governments. They are highly sophisticated and often target critical infrastructure, industries, or political systems. Unlike ordinary cybercrime, these attacks are strategic, resource-intensive, and have far-reaching consequences.
Motivations include espionage, economic disruption, and geopolitical influence. Famous examples include:
- Stuxnet (2010): A joint U.S.-Israel operation that disrupted Iran’s nuclear facilities.
- Russian DNC Hack (2016): Targeted the Democratic National Committee during the U.S. elections.
- WannaCry (2017): Attributed to North Korea, this ransomware spread globally demanding Bitcoin payments.

The Evolution from Ransomware to State-Sponsored Cyberattacks
Ransomware initially targeted individuals or small groups for financial gain. However, the emergence of state-sponsored cyberattacks transformed these threats into powerful tools of national strategy. Governments now use ransomware for espionage, economic disruption, and political influence.
As nations rely on digital infrastructure, ransomware has become a critical weapon in the geopolitical arena. Protecting against state-sponsored cyberattacks is no longer just a technological challenge—it is a matter of national security.
Combating Cyberattacks
Addressing state-sponsored cyberattacks requires technology, collaboration, and strategy. International organizations such as the United Nations and INTERPOL coordinate intelligence sharing and promote digital norms. The UN, for instance, emphasizes protecting critical infrastructure and discouraging offensive cyber operations.
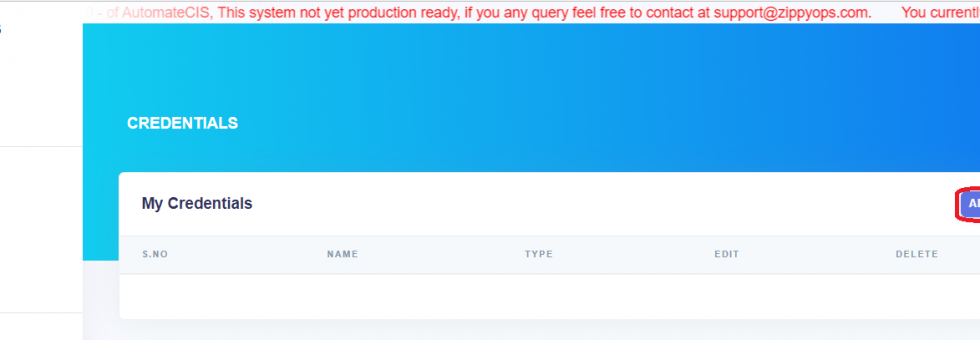
Companies like ZippyOPS assist organizations in strengthening defenses. They provide consulting, implementation, and managed services covering DevOps, DevSecOps, DataOps, Cloud, Automated Ops, AIOps, MLOps, Microservices, Infrastructure, and Security. Learn more through their services, solutions, and products.
Cybersecurity Best Practices Against Cyberattacks
Robust cybersecurity measures are essential. Use strong passwords, enable multi-factor authentication, and keep software updated. Employee awareness through training and phishing simulations is equally critical.
Data backup ensures resilience. Regular offline or cloud backups allow restoration without paying ransom. ZippyOPS integrates security into cloud, automated operations, and microservices systems, providing end-to-end protection. Check their YouTube channel for practical demos.
Conclusion
State-sponsored cyberattacks have escalated from simple ransomware to sophisticated nation-level threats. Their impact on global infrastructure, politics, and the economy is profound. Consequently, organizations must adopt advanced security practices and leverage expert guidance.
Partnering with ZippyOPS ensures protection against complex threats through consulting, implementation, and managed services across DevOps, DevSecOps, Cloud, and security frameworks. Safeguard your organization today by contacting sales@zippyops.com.