Pipeline as Code Security: Best Practices & Mitigation
Pipeline as Code has revolutionized CI/CD workflows by allowing developers to define and manage pipelines through code. This approach improves consistency, scalability, and version control. However, like any codebase, Pipeline as Code scripts can contain vulnerabilities that compromise software delivery. Therefore, understanding common risks and implementing effective safeguards is critical for secure deployments.
Common Security Vulnerabilities in Pipeline as Code
Exposure of Sensitive Information
Hardcoding credentials, API keys, or other secrets in PaC scripts is a major risk. If these scripts are exposed in repositories or logs, attackers can gain access to critical systems. For example, embedding YOUR_API_KEY directly in a YAML pipeline can lead to unauthorized access:
stages:
deploy:
stage: deploy
script:
- curl -H "Authorization: Bearer YOUR_API_KEY" https://api.example.com/deployInadequate Access Controls
PaC scripts with weak access permissions can be modified or executed by unauthorized users. This exposes systems to code injection, malicious deployments, or accidental misconfigurations.
Untrusted Third-Party Plugins
Using unverified plugins or libraries introduces vulnerabilities. Attackers can exploit flaws or malicious code within these dependencies, compromising the entire pipeline. Regular security reviews of third-party components are essential. More guidance is available from the CIS DevOps Security Framework.
Lack of Input Validation
Scripts that accept unchecked input can be targets for injection attacks. For instance, passing user-provided environment parameters directly into shell commands can execute harmful operations if not validated:
pipeline {
agent any
stages {
stage('Deploy') {
steps {
script {
def environment = params.ENVIRONMENT
sh "deploy.sh ${environment}"
}
}
}
}
}Insufficient Logging and Monitoring
Without detailed logging, unauthorized modifications or access may go undetected. Consequently, delayed detection increases the risk of prolonged exposure and damage.
Mitigation Strategies for Pipeline as Code
Implement Secrets Management for Pipeline as Code
Use secure secrets management solutions rather than hardcoding credentials. Tools like HashiCorp Vault or cloud-native secret managers reduce exposure while enabling automated pipelines.
Enforce Strict Access Controls for Pipeline as Code
Apply the principle of least privilege. Only grant users the permissions necessary to execute or modify pipelines. Regularly audit and update permissions as team roles evolve.
Vet and Monitor Third-Party Dependencies for Pipeline as Code
Before integrating external plugins or libraries, conduct thorough security assessments. Keep dependencies updated and monitor for any reported vulnerabilities.
Incorporate Input Validation for Pipeline as Code
Validate all inputs to prevent injection attacks. For example, restrict environment parameters to allowed characters:
pipeline {
agent any
stages {
stage('Deploy') {
steps {
script {
def environment = params.ENVIRONMENT
if (environment ==~ /^[a-zA-Z0-9_-]+$/) {
sh "deploy.sh ${environment}"
} else {
error "Invalid environment parameter."
}
}
}
}
}
}Implement detailed logging for all pipeline actions. Use monitoring tools to detect anomalies, trigger alerts, and respond promptly to security events.
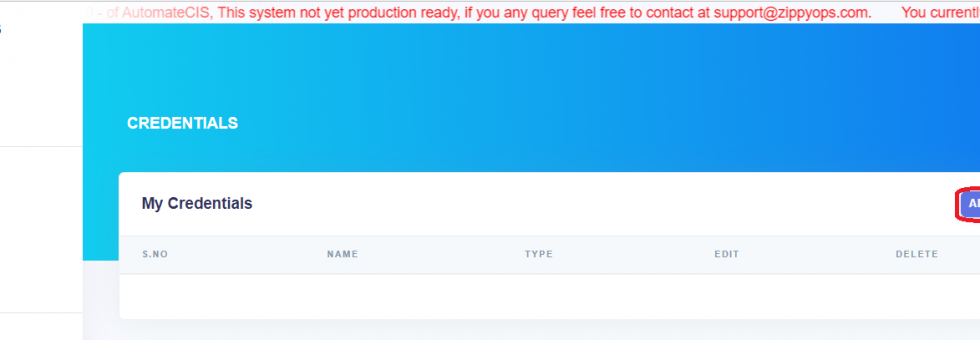
How ZippyOPS Secures Pipeline as Code
ZippyOPS provides consulting, implementation, and managed services for DevOps, DevSecOps, DataOps, Cloud, Automated Ops, AIOps, MLOps, Microservices, Infrastructure, and Security. Our expertise ensures CI/CD pipelines are secure, efficient, and compliant.
We help organizations implement zero-trust access controls, secure secrets management, and automated monitoring. Our solutions integrate seamlessly with modern infrastructure and cloud environments. Explore more:
For demonstrations, visit our YouTube Playlist.
Conclusion
Pipeline as Code brings efficiency and consistency to CI/CD, but it also introduces security risks. By implementing secrets management, strict access controls, vetted third-party components, input validation, and robust logging, organizations can significantly reduce vulnerabilities.
Partnering with ZippyOPS ensures your pipelines are both secure and scalable, allowing teams to focus on delivering high-quality software without compromising integrity. For expert guidance, contact sales@zippyops.com.