Unsupervised Learning for Encrypted Traffic
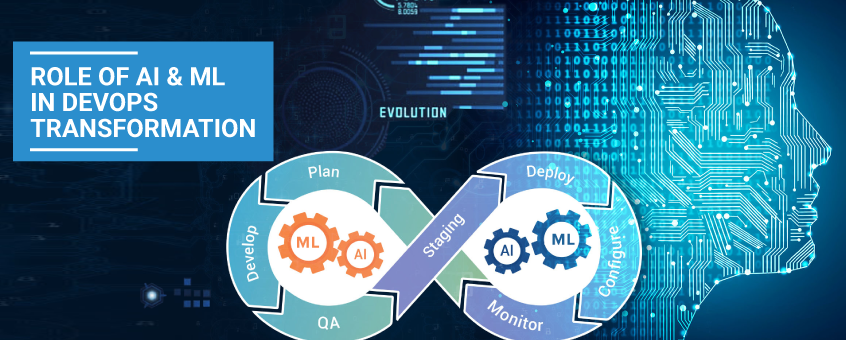
Discover how unsupervised learning methods like clustering, dimensionality reduction, and anomaly detection analyze encrypted network traffic without decryption. Learn how ZippyOPS, a leading microservice consulting provider, enhances security with cutting-edge DevOps, AI Ops, and Microservices solutions.